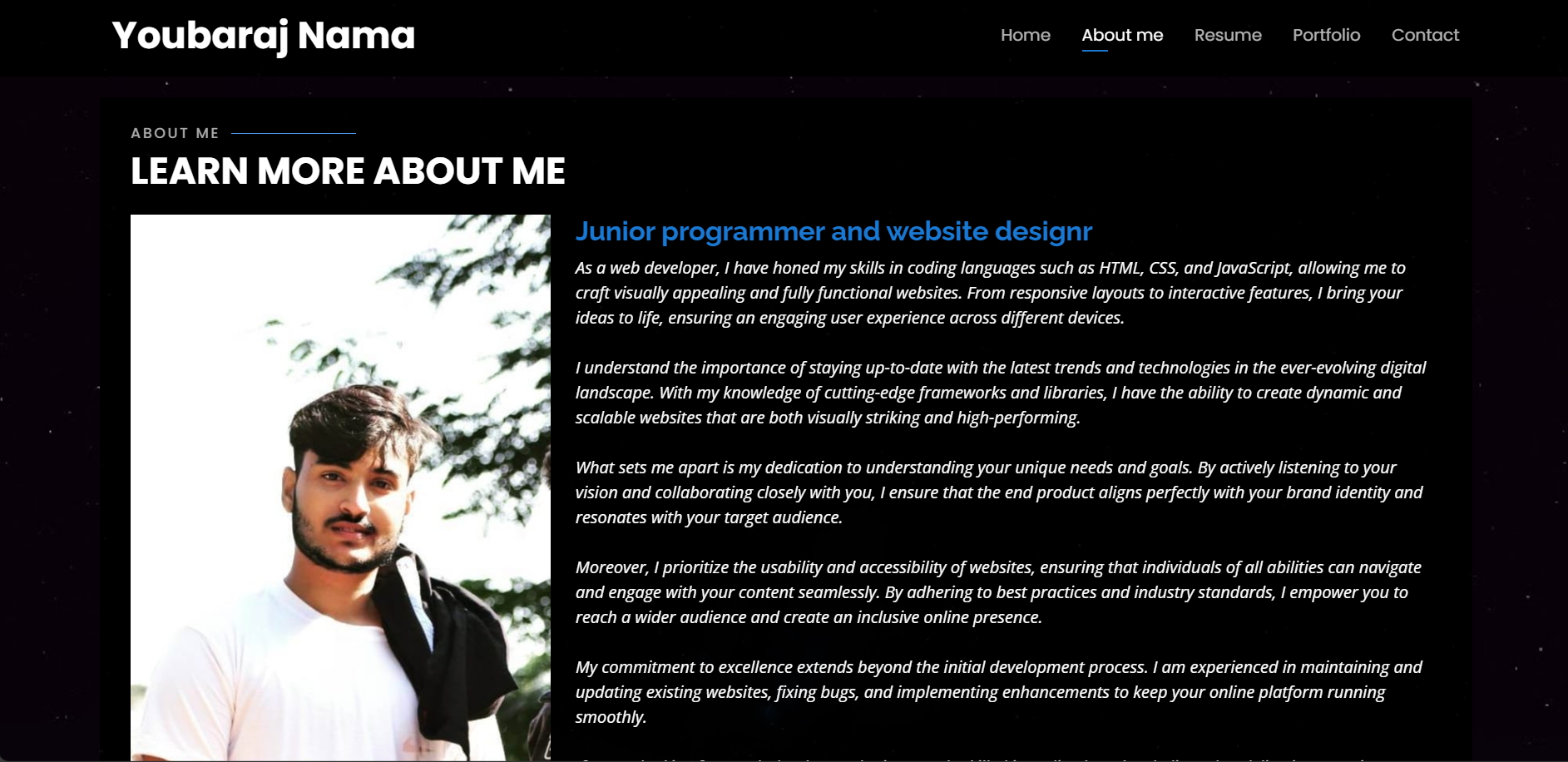
Web Designing Portfolio
A showcase of my web design projects including responsive layouts, UI/UX designs, and front-end development work.
Visit Portfolio

Firewall configuration, IDS/IPS, VPNs, and secure network architecture.

Ethical hacking, vulnerability scanning, and exploit development.

Threat analysis, containment, eradication, and recovery processes.

Encryption algorithms, PKI, SSL/TLS, and secure communications.

AWS, Azure, GCP security best practices and compliance.

Log analysis, threat detection, and security event correlation.

Python, Bash scripting, PowerShell for automation and tooling.

GDPR, HIPAA, PCI-DSS, and cybersecurity frameworks.
Fast and accurate data entry with attention to detail.
UI/UX design, responsive layouts, and front-end dev.
A showcase of my web design projects including responsive layouts, UI/UX designs, and front-end development work.
Visit Portfolio
Developed a custom IDS using Snort and Suricata to monitor and alert on suspicious network activity in real-time.
View on GitHub
Created an interactive platform to educate employees on phishing threats, including simulated phishing campaigns and quizzes.
View on GitHub
Built a Python-based tool to automate scanning of web applications for common vulnerabilities like SQLi and XSS.
View on GitHub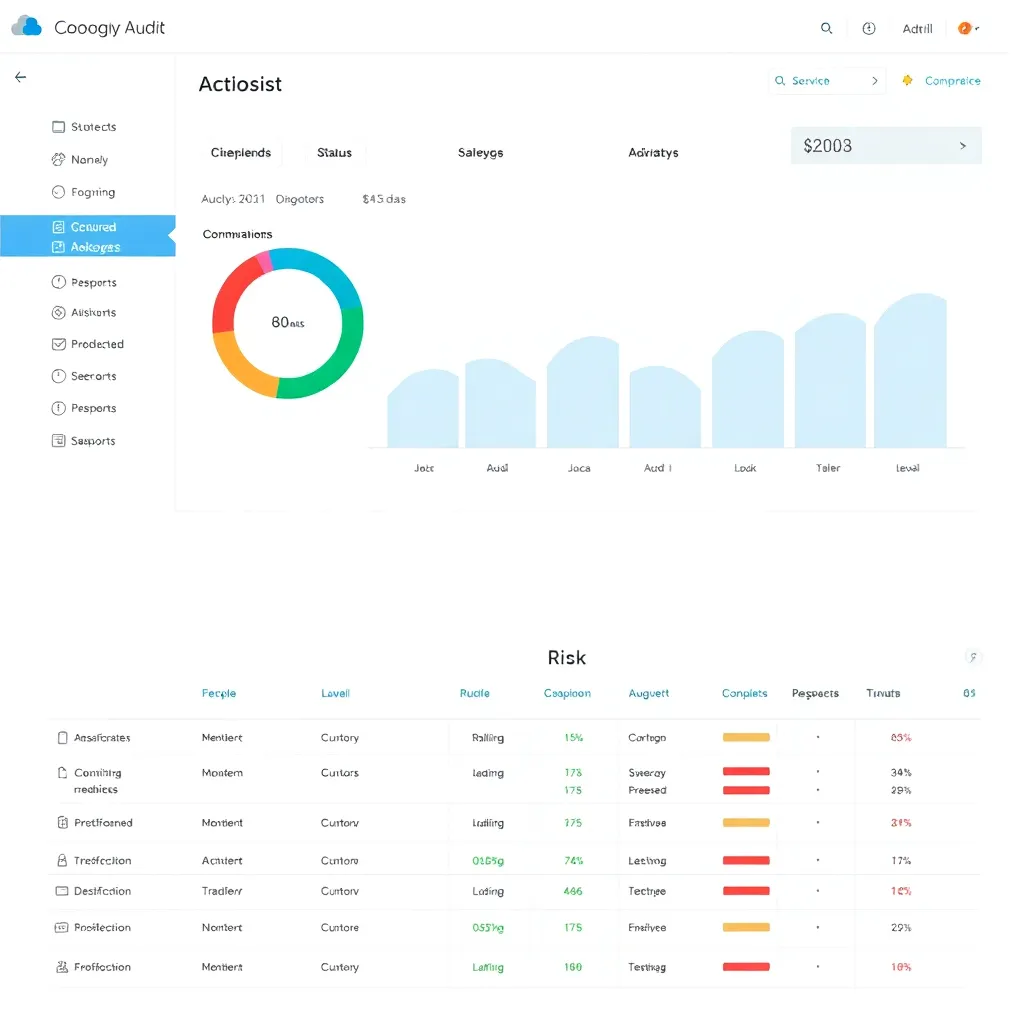
Developed a tool to audit AWS and Azure environments for security misconfigurations and compliance violations.
View on GitHub
Integrated multiple log sources into a SIEM platform with custom alert rules to detect advanced persistent threats.
View on GitHub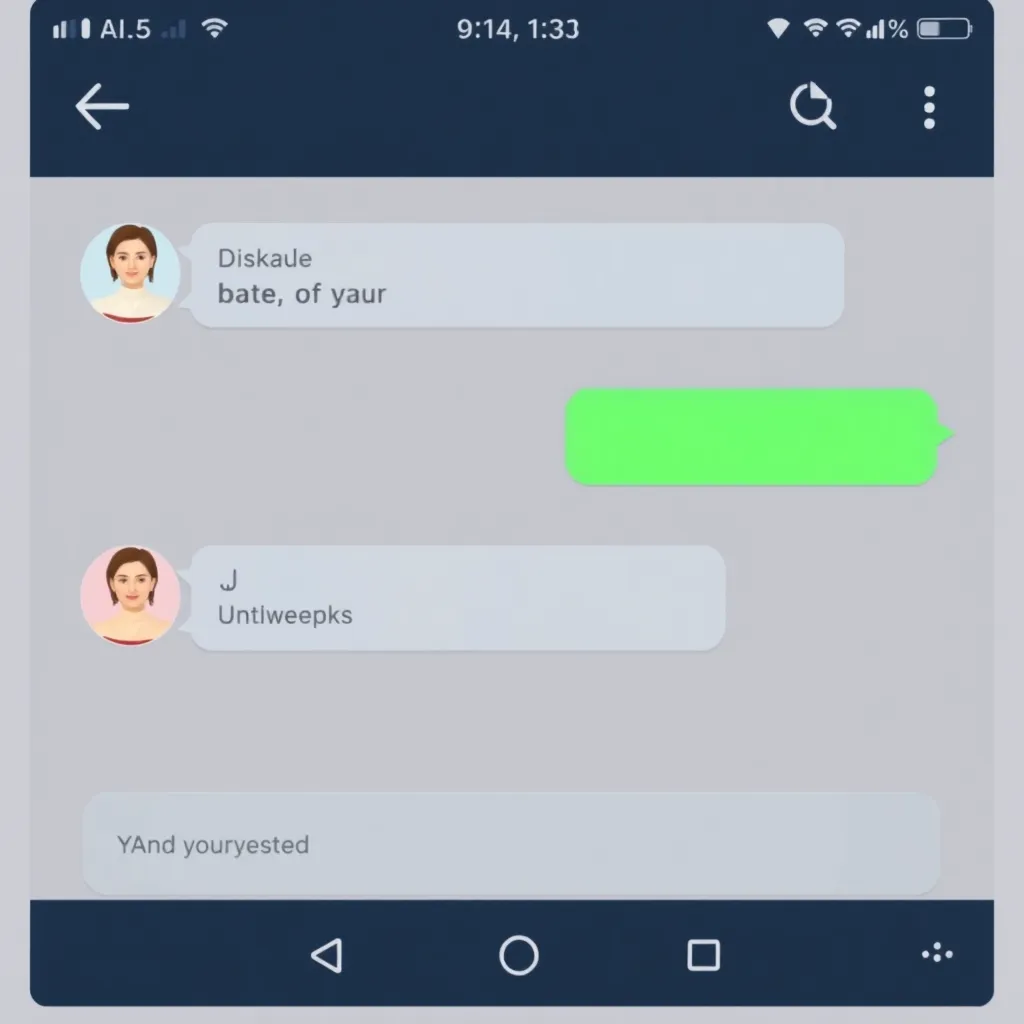
Designed and implemented an encrypted messaging app using AES and RSA for secure communications.
View on GitHub
Created a dashboard aggregating threat feeds and visualizing attack trends for proactive defense.
View on GitHub
Developed a script to automatically encrypt and securely store backups using GPG and cloud storage.
View on GitHub



An in-depth analysis of emerging cyber threats and how organizations can prepare for them.
Read More
Tips and methodologies to conduct effective and ethical penetration tests.
Read More
Exploring common cloud security pitfalls and how to mitigate risks effectively.
Read More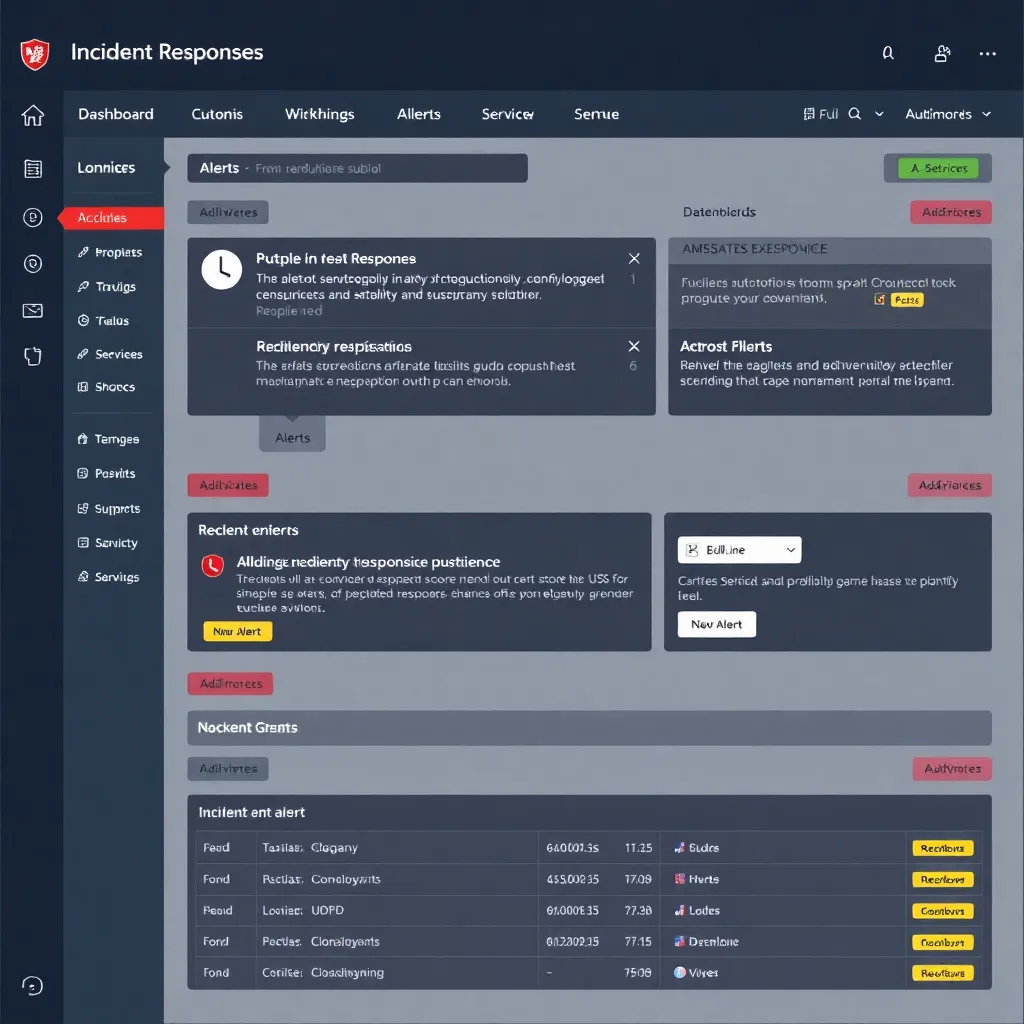
How automation is transforming incident response and improving security operations.
Read MoreOr reach me directly at youbarajnama@outlook.com
Phone: +91 9366176746